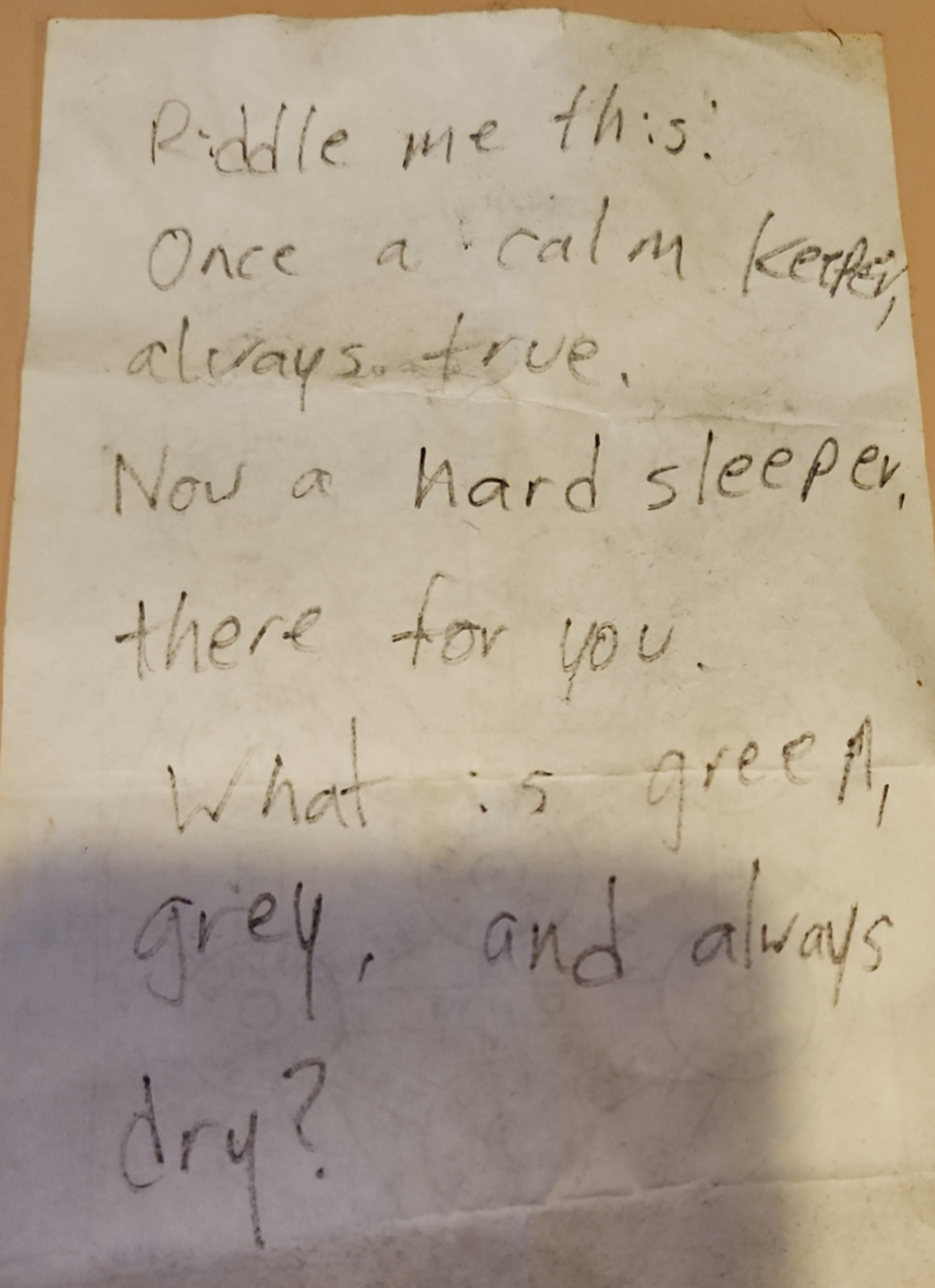
The discovery of an unexplained message within a residential environment—often categorized by social media as a "cryptic note"—is rarely a supernatural event. It is a data-processing failure. When a tenant encounters an unreadable script or a concealed message behind wallpaper or under floorboards, the "unsolvable" nature of the artifact typically stems from a lack of structural analysis rather than an inherent lack of meaning. To resolve these anomalies, one must apply the principles of historical linguistics, physical forensics, and steganography.
The viral fascination with "unsolvable" notes usually highlights a gap between amateur observation and systematic inquiry. Most residential mysteries collapse under the weight of three specific variables: the physical substrate, the encoding method, and the chronological context.
The Tri-Axis Framework of Message Forensics
To evaluate any mysterious artifact found in a home, the analyst must categorize the evidence into three distinct silos. Failure to isolate these variables leads to speculative bias, where the observer projects personal fears or cultural tropes onto the data.
1. Substrate Degradation and Environmental Noise
The medium is often mistaken for the message. In older properties, chemical reactions between ink and lead-based paint, or the oxidation of cellulose in paper, can warp legible script into what appears to be occult symbols. Before attempting to "decode" the content, the physical state of the material must be assessed.
- Ink Migration: Over decades, certain pigments bleed into the fibers of the wall, creating "ghosting" effects that look like intentional abstractions.
- Microbial Interference: Mold patterns (specifically Stachybotrys chartarum) can grow in linear formations along structural beams, mimicking handwriting to the untrained eye.
2. Linguistic and Symbolic Encoding
If the markings are determined to be intentional, the next phase is identifying the system of notation. "Cryptic" is often a synonym for "unfamiliar."
- Shorthand Systems: Many "unsolvable" notes from the mid-20th century are simply Pitman or Gregg shorthand. These are high-speed phonetic scripts that look like abstract squiggles to those born after the digital transition.
- Trade Vernacular: Construction workers frequently leave marks—often called "carpenter’s marks" or "witness marks"—to align joists or indicate plumbing runs. To a layman, these look like a series of runes or tally marks.
- Ciphers vs. Codes: A cipher replaces individual letters; a code replaces entire ideas. Most residential notes are ciphers (substitution or transposition) created by previous inhabitants for privacy, often regarding financial records or personal grievances.
3. Chronological Contextualization
A note is a snapshot of a specific socio-economic moment. Its meaning is tethered to the year it was concealed. A note mentioning "the gold under the stairs" in 1930 has a vastly different risk-reward profile than a similar note from 1990. The former suggests a Great Depression-era distrust of banks; the latter suggests a potential prank or a delusional episode.
The Cost of Information Asymmetry in Tenancy
The "mystery" of a cryptic note is a byproduct of information asymmetry. The current renter possesses the physical object but lacks the historical metadata of the property. This gap creates a vacuum filled by "the crowd," which rarely applies rigorous logic.
The Probability of the Hoax
In the modern digital economy, the "unsolvable note" acts as a high-yield engagement asset. The incentive structure of social media platforms rewards the creation of "creepypasta"—fictionalized accounts of mysterious finds. When analyzing these cases, the probability of a hoax ($P_h$) must be weighed against the probability of a genuine historical artifact ($P_a$).
$P_h$ increases significantly if:
- The discovery is documented with high-production-value video.
- The "note" uses tropes common in horror cinema (e.g., "don't open the basement").
- The uploader refuses to provide high-resolution, static images for professional linguistic analysis.
Decipherment Protocols for High-Ambiguity Scripts
If an artifact passes the initial filter for authenticity, the resolution requires a tiered technical approach.
Tier 1: Multi-Spectral Imaging
Human vision is limited to a narrow band of the electromagnetic spectrum. Many "unsolvable" notes are simply faded. By using ultraviolet (UV) or infrared (IR) light, one can often reveal ink layers that have been painted over or have faded due to UV exposure. This is the same technology used to read the Archimedes Palimpsest.
Tier 2: Frequency Analysis
If the note is written in a substitution cipher, the "cryptic" nature is a mathematical problem. In English, the letter 'E' appears with a frequency of approximately 12.7%. By counting the recurrence of specific symbols, an analyst can map them to the English alphabet. This ignores the "spooky" aesthetic of the symbols and treats the note as a simple data set.
Tier 3: Provenance Mapping
The physical location of the note within the architecture provides the final clue.
- Behind Chimney Breasts: Often related to heat-based protection or "witch bottles" in older folk traditions (Apotropaic magic).
- Under Floorboards: Usually concealment of tangible assets or illicit materials.
- Inside Door Frames: Frequently related to structural measurements or house-blessing traditions (such as the Jewish Mezuzah or European "house marks").
The Structural Fallacy of the "Unsolvable"
The primary reason a note remains "unsolved" is not its complexity, but the medium of its distribution. Social media comments sections are optimized for speculation, not deduction. They lack the peer-review mechanisms necessary for cryptographic resolution. When a "mystery" goes viral, the noise-to-signal ratio makes the truth harder to extract.
Most "cryptic" notes are mundane. They are grocery lists in obsolete shorthand, contractor notes for a renovation that never happened, or the remnants of a child’s private game. The aura of mystery is a projection of the observer’s inability to categorize the data.
To resolve a residential mystery, one must strip away the narrative. Stop looking for a "story" and start looking for a system. If the script is repetitive, it is a language. If it is erratic, it is a physical byproduct of decay or a hoax. If it follows a grid, it is a map or a ledger.
The strategic path forward for any tenant finding such an artifact is to bypass the public forum and move directly to specialized databases. Use the "Pen, Pencil, and Paper" (P3) method of transcription to isolate symbols, then cross-reference with the International Association for Cryptologic Research or local historical societies. The solution is rarely found in the comments; it is found in the archives.
Finalize the investigation by determining the physical age of the paper through radiocarbon dating or, more practically, by identifying the manufacturer's watermark. This establishes the "Earliest Possible Date" (EPD), effectively narrowing the list of potential authors from "anyone in history" to a specific decade of residents. Logic, not speculation, closes the file.